Built in server
Every iGuard Biometric / smart Card Security Product has a built-in Internet Server that allows all the computer systems in the company network to directly and concurrently access the unit using any kind of Internet Browser, for example Microsoft Ie ,Netscape Navigator. Various computer systems such as Apple Mac, Windows Linux devices can use the device. Absolutely no supplementary software programs are required. Therefore, irrespective of you being in an airport terminal or in lodge, you can at all times see if your workers happen to be in the office or otherwise. You can also control, alter or eliminate their entry rights for your office via web connection provided your iGuard Biometric / smart Card Security Product is attached to an external Ip or your own network through a VPN link that is obtainable from your area.
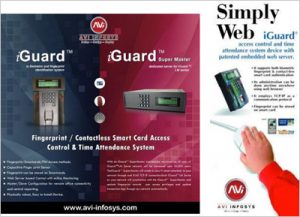

Multiple confirmation methods Several verification techniques:
With iGuard, customers can be validated as well as confirmed through Fingerprint, Smartcard or Passwords. As well as depending on the various time periods, you will be able to set up the iGuard through which the customers can simply present their smartcard to be approved (such as during busy period), or make the high safety finger prints verification a requirement (for example after work hours or throughout weekends as well as holidays).
access privileges:
if you are able to effortlessly and handily allocate different entry rights for your workers, you will be able to plan your own security much better and increase the efficiency of your human resources . Along with the built-in Web Host technology, iGuard enables you to handle the entry rights of every individual worker or a number of employees effortlessly anytime, anyplace using any kind of web-enabled computers or even mobile devices.
For instance, you can allocate the staff people in the advertising department the l rights to enter the office property during Mondays to Fridays from 9 to 5 only, or even prevent a specific worker from entering the pc server space.
Reports:
iGuard consists of three built-in raw reports: Entry Log, Work Report & Every day In/Out report, that may be accessed through any web-enabled pc with internet browser. the information is obtainable and held in Microsoft Stand out format as well as in plain textual content format. Additionally, the entry records could be saved in any kind of PC within the network within the popular ODBC data source format in real-time manner, along with other applications which can conveniently have the information in the ODBC (the required software program, iServer.exe, is available without charge in our website for downloading).
Affordable:
All of the necessary software and hardware is built-in the device, such as the hardware for connecting the system towards the corporate system. All you have to perform is to plug-in the renowned RJ-45 network cable onto the rear of the gadget. No other equipment and cabling are necessary.
In comparison, all other current security methods use the aged RS232 & RS485 wiring program to connect to the dedicated computer systems (not to the organization network), also it usually entails a lot of extra cabling works.
small area space:
iGuard is stylishly designed which is to be mounted on the wall with very small impact. In fact, it’s the smallest stand-alone biometrics gadget obtainable in the marketplace these days. It can be installed easily as well as conveniently with out requiring much space.
User-Friendly:
iGuard is an Internet-Ready Security System, and is the foremost and the only security item in the market that utilizes TCP/IP as the process to communicate along with other iGuards and the rest of the world. The process enables the unit to straight connect to the organization network through the existing cable television wiring.
Because the TCP/IP protocol may be the Internet protocol, this allows just about all computers within the corporate system to access the unit using the Internet browser software. Consequently, users don’t need to learn in order to make use of a new software program for accessing as well as administering the unit, with assurance that most customers can start using device within a few minutes.
In contrast, other similar security methods use complex protocol & cabling, and complicated software is necessary to access scalping strategies. And for match ups purposes.
Master/Slave settings:
Multiple iGuard models can be set up as a Master/Slave system. Under this particular configuration, one iGuard would be designated as the master, and all additional units tend to be configured as slaves. When a person enrolls in anyone of these iGuard models, his / her personal information, such as the fingerprint info, would be duplicated to all additional iGuard units within the same master / slave network, therefore the same person does not need to sign up multiple times to have the entry rights to any or all these models.
` Remote Doorway Relay:
This particular controller additionally increases the security scale by manipulating the door way from inside the premises. With this particular optional control, the iGuard transmits a special transmission to this control to open the doorway, rather than straightaway opening the doorway with the inner relay. As this optional control is set up inside the property, it is now impossible for the intruders to get into the actual premises, even in the situation where they rupture the iGuard.
Email us if there are any broken links, navigation issues, missing graphics or download issues, please help us to improve our website.
